Why Governments Trust Secure Elements For Your Passport, Bank Card, and ID

Core Insights
Secure elements, tamper-resistant chips found in passports, credit cards, and national IDs, were adopted by governments and financial institutions to combat widespread fraud and forgery that plagued earlier technologies like magnetic stripes and paper documents. By securely storing private cryptographic keys, these chips make it economically and technically unfeasible for attackers to clone or forge credentials, a logic that also underpins the security of hardware wallets for cryptocurrencies. The same high standards and rationale that protect billions of official documents and cards now similarly safeguard digital assets in consumer hardware wallets.Both your passport and your credit card contain chips. If you have a government-issued national ID, it probably has one too. Every time you tap your card at a payment terminal or scan your passport at a border, a secure element is doing the cryptographic work that makes those transactions trustworthy.
Governments and financial institutions have been deploying secure elements at a massive scale for over two decades. They didn't arrive at this decision by accident, and they didn't stay with it out of inertia.
After extensive evaluation of the alternatives, they concluded that secure elements are the most practical solution to a very specific problem: how do you protect a secret in a physical object that will spend its entire life in the hands of people who might want to compromise it?
The specific problems Secure Elements solve
To understand why secure elements ended up in passports and credit cards, you have to understand what was happening before they existed and what attacks were actually costing governments and banks real money at a real scale.
Credit card fraud before the chip
Before EMV chip cards became standard in the 1990s and 2000s, credit and debit cards stored data on magnetic stripes. That stripe contained the card number, expiration date, and a service code. It could be read by any magnetic stripe reader, including cheap, portable skimming devices that criminals attach to ATMs and payment terminals.
Card skimming was a massive, industrial-scale fraud problem. Organized criminal groups operated networks of skimmers across entire countries. The stolen data was easy to copy onto blank cards. The cards could then be used anywhere that accepted magnetic stripe transactions. The fraud scaled effortlessly because copying a magnetic stripe costs almost nothing and requires no technical expertise.
The banking industry's problem was that fraud was cheap to execute, impossible to scale defenses against, and the cumulative losses were enormous. By the early 2000s, card fraud was costing the global banking industry billions of dollars annually.
Passport forgery before biometric chips
Paper passports faced a similar structural problem. A skilled forger with the right equipment could produce a convincing fake. Improving physical security features helped, but it was an arms race: every new feature governments added eventually got replicated by criminal operations with sufficient resources and motivation.
The deeper problem was that border officers had no way to verify a passport's authenticity beyond visual inspection. There was no cryptographic proof that a document was genuine
A private cryptographic key
Secure elements solved both problems by introducing something that cannot be copied: a private cryptographic key stored in tamper-resistant hardware, used to sign transactions or authenticate the document in a way that only the genuine chip can produce.
A cloned magnetic stripe is identical to the original; there's nothing the payment terminal can check to distinguish them. However, a cloned EMV chip transaction fails because it requires a cryptographic signature that only the genuine chip can generate. You'd need to extract the key from the chip and replicate it, which requires a laboratory, not a card reader.
A forged paper passport can look identical to the real thing. A forged ePassport fails at the border scanner because the chip's digital signature over the biometric data was issued by the government's own signing key, and that signature can be cryptographically verified.
Creating a fake that passes verification requires breaking the signing chain, which is a fundamentally different and much harder problem than printing convincing security features.
Why decide on Secure Elements?
The decision to deploy secure elements at scale was driven by economic and political considerations. Governments and banks had to weigh the cost of transitioning hundreds of millions of cards and documents against the fraud losses they were absorbing.
They had to choose a technology that would work reliably in the hands of ordinary people, in environments ranging from supermarkets to remote border crossings, in devices that cost a few dollars to manufacture.
The secure elements used in passports, national ID cards, and banking infrastructure carry CC EAL5+ or EAL6+ certification; the same standard discussed earlier in this series.
Governments mandated these certification levels because the evaluation process provides independent evidence that the chip resists the most sophisticated non-classified attack techniques known at the time of evaluation.
In practice, this means cracking the chip requires either classified capabilities or a level of academic research investment that takes months, produces published papers, and is conducted by a very small number of people worldwide. Neither of these represents a scalable attack on the general population of passport holders or cardholders.
Why does the same logic apply to your wallet?
The parallel between government document security and hardware wallet security is closer than it might first appear. The problems are structurally identical.
A government issuing a passport needs to protect a cryptographic credential in a physical object that its citizens will carry for 10 years, examine at foreign border crossings, and occasionally lose or steal. The citizen is not a security expert. The credential needs to remain protected without requiring any active security behavior from the person carrying it.
A hardware wallet user needs to protect a private key in a physical device that will be used regularly, potentially carried around, and occasionally lost or stolen. The user may not be a security expert. The key needs to remain protected against remote attackers, opportunistic thieves, and anyone who finds or steals the device.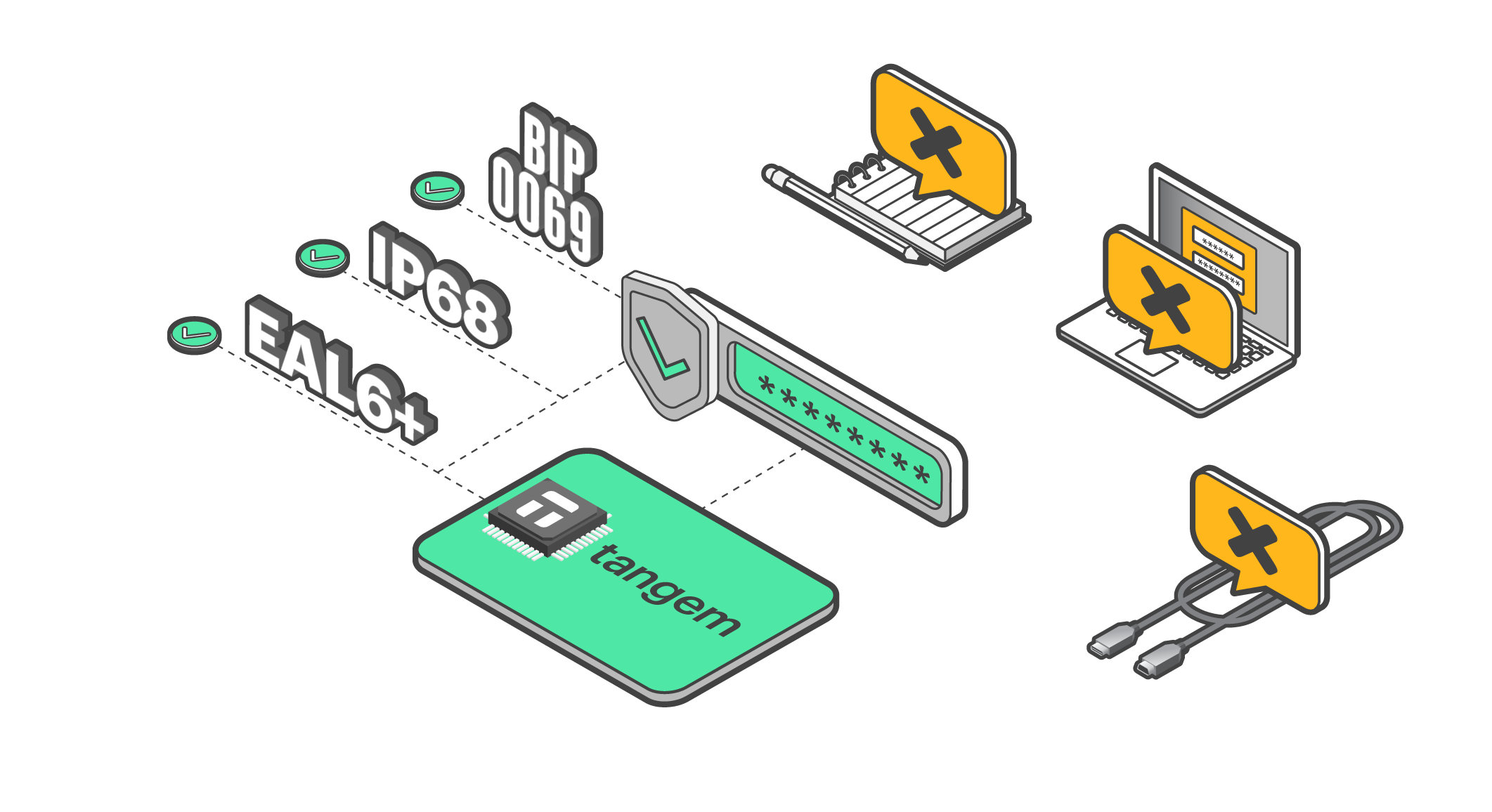 In both cases, the secure element's job is the same: make the cost of extracting the protected secret so high that it's economically irrational for the realistic threat population. Both use the same certified chips from the same manufacturers. Both depend on the same physical security architecture. The government's rationale for trusting the technology directly applies to the crypto user's situation.
In both cases, the secure element's job is the same: make the cost of extracting the protected secret so high that it's economically irrational for the realistic threat population. Both use the same certified chips from the same manufacturers. Both depend on the same physical security architecture. The government's rationale for trusting the technology directly applies to the crypto user's situation.