What is a Private Key, How It Works, and How to Protect It

- AI summary
- What Is a Private Key in Crypto?
- Private Key vs. Password: Why It's Not the Same Thing
- What Is a Public Key and How Does It Relate?
- How Are Private and Public Keys Generated?
- How Do Private Keys Work in a Transaction?
- What Is a Seed Phrase and How Does It Relate to a Private Key?
- Why You Should Never Share Your Private Key
- Where and How Should You Store a Private Key?
- Hot Wallets vs. Cold Wallets: A Quick Overview
- How Tangem Wallet Solves the Private Key Problem
- Common Private Key Mistakes and How to Avoid Them
- Frequently Asked Questions
- Final Thoughts
AI summary
This article explains the critical role of private keys in cryptocurrency ownership, detailing how they work, why they must be kept secure, and the dangers of losing or exposing them. It compares private keys to passwords, clarifies their relationship to public keys and seed phrases, and outlines best practices for storage—emphasizing hardware wallets like Tangem, which securely store keys without requiring a seed phrase. Ultimately, the article stresses that understanding and protecting your private key is essential to truly owning and safeguarding your crypto assets.
If you own any cryptocurrency, there's one concept you absolutely need to understand: the private key. It's the foundation of everything. Lose it, share it, or store it carelessly, and you could lose your crypto permanently, with no way to get it back. This guide explains what a private key is, how it relates to a public key, why it matters, and how to keep it safe. No unnecessary jargon. Just the important information you need to know.
What Is a Private Key in Crypto?
A private key is a long, randomly generated string of numbers and letters that gives you access to your cryptocurrency. Think of it like the master password to a vault. Whoever holds the private key controls the funds in the associated wallet. Here's what a Bitcoin private key looks like in practice:
5Kb8kLf9zgWQnogidDA76MzPL6TsZZY36hWXMssSzNydYXYB9KF
No human could realistically memorize it. Mathematics makes it unique and almost impossible to guess. In fact, the number of possible private key combinations exceeds the total number of atoms in the observable universe.
A private key gives you the ability to:
- Access your crypto wallet and view your balance
- Authorize transactions by creating a digital signature
- Prove ownership of your funds on the blockchain
Without a private key, you have no real control over your crypto, even if the funds technically exist at a blockchain address. That principle sits at the core of what it means to truly “own” cryptocurrency.
Private Key vs. Password: Why It's Not the Same Thing
Beginners often assume a private key works like a regular password and can be reset if they forget it. It doesn’t. Blockchain is decentralized, meaning there's no company, bank, or support team holding a spare copy. No one can reset it for you. The system generates your private key once. If you lose it, you lose access to your funds forever, which makes protecting it the most important responsibility in crypto ownership.
What Is a Public Key and How Does It Relate?
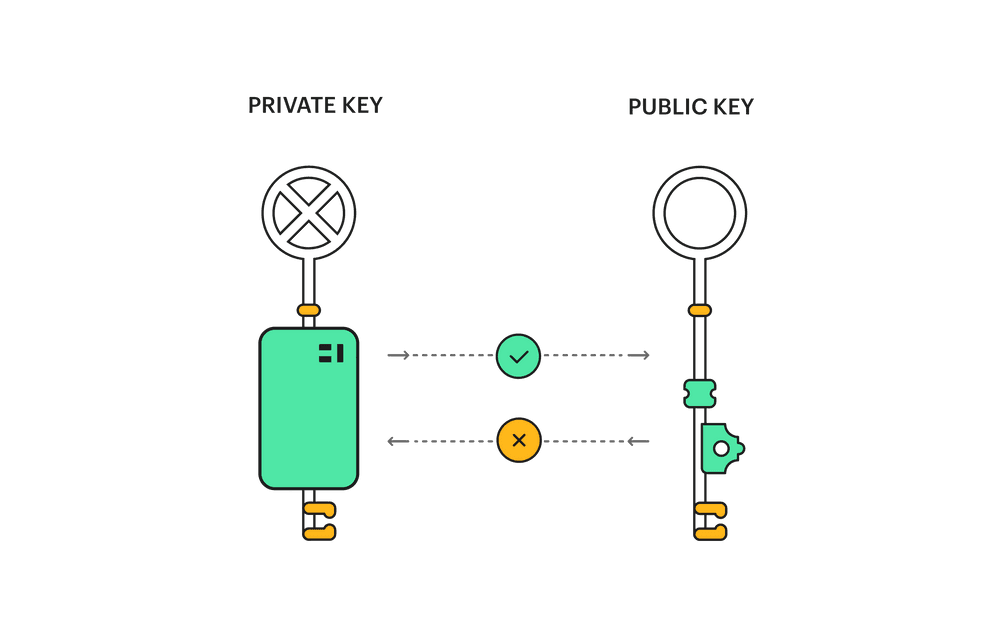
Every private key has a matching public key. These two always come as a pair, and together form the backbone of public-key cryptography, the system that keeps blockchain transactions secure.
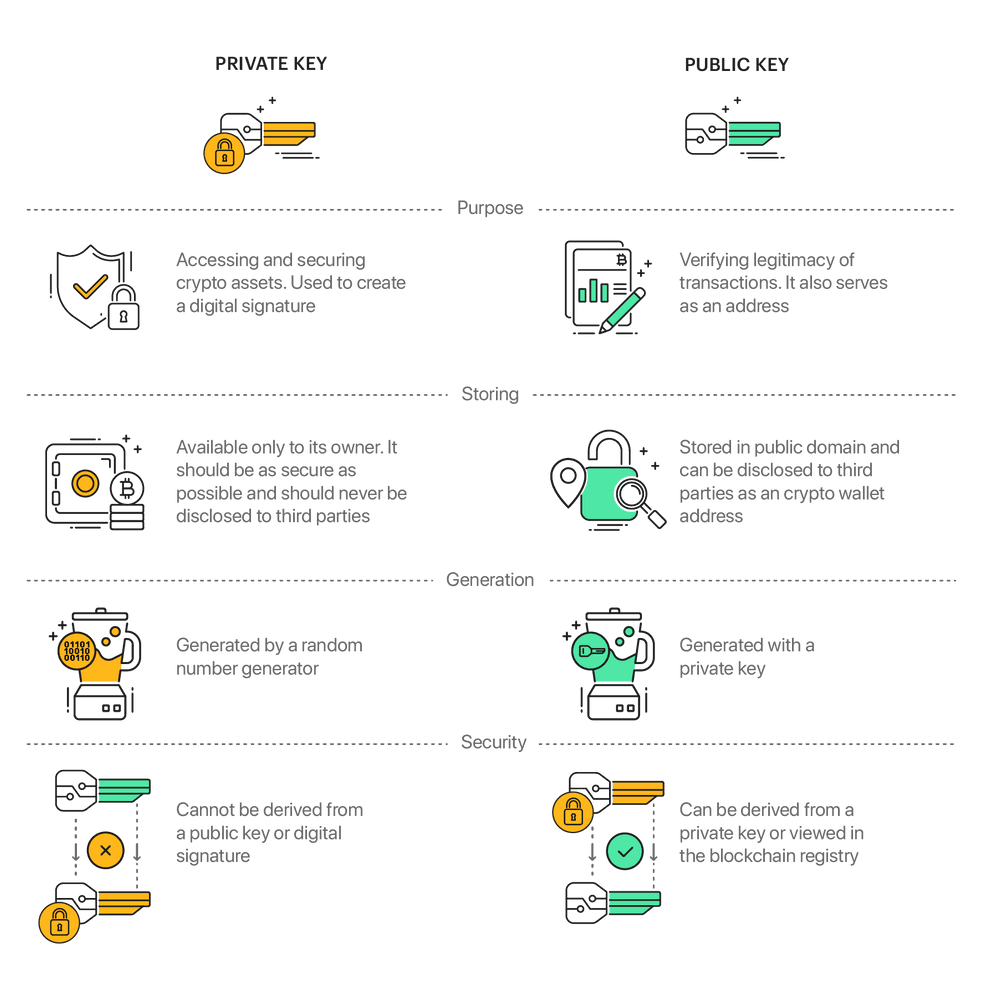
Key Distinction | Private Key | Public Key |
What it is | A secret, randomly generated number | A number derived from the private key |
Who sees it | Only you | Anyone |
What it does | Signs (authorizes) transactions | Verifies the signature on transactions |
Can it generate the other? | Yes, generates the public key | No, cannot reverse-engineer the private key |
Shareable? | Never | Yes, safe to share |
The relationship between the two is one-way by design. You can always generate a public key from a private key. Still, it is mathematically impossible to reverse-engineer the private key from the public key, which is what makes the system secure.
How Are Private and Public Keys Generated?
When you create a crypto wallet, the software generates a private key using a random number generator. This randomness (called entropy) is critical. If a system generates a key from a predictable or low-quality random number, attackers could guess it. Once the private key exists, the public key is derived from it using elliptic curve cryptography (ECC). Bitcoin, for example, uses a specific elliptic curve, secp256k1.
The process works in three broad steps:
Step 1: A random private key is generated. The wallet picks a massive random number. This is your private key.
Step 2: The public key is derived. A mathematical operation (point multiplication on an elliptic curve) converts the private key into a corresponding public key. This step is one-directional — you can go from private to public but never back.
Step 3: A wallet address is created. The public key is further processed (hashed and encoded) to produce the human-readable wallet address you share with others to receive funds, for example, a Bitcoin address starting with 1, 3, or bc1.
Your public address is what you share when someone wants to send you crypto. It's derived from the public key but is even shorter and easier to handle.
How Do Private Keys Work in a Transaction?
Every time you send cryptocurrency, your private key is doing important work behind the scenes. Here's what happens:
Step 1: You initiate a transaction
You open your wallet and enter the amount of crypto to send and the destination address. At this point, the transaction exists as unsigned data.
Step 2: Your wallet signs the transaction
Your wallet software uses your private key to create a digital signature, a unique cryptographic stamp that proves you authorized this transaction. Importantly, this signature doesn't expose your private key. It only proves you have it.
Step 3: The network verifies it
Your wallet broadcasts the transaction to the blockchain network. Nodes (computers participating in the network) use your public key to verify the digital signature. If the math checks out, the transaction is confirmed and added to the blockchain. Your private key never leaves your device during this entire process. This is the elegance of asymmetric cryptography: you can prove ownership without ever revealing the secret itself.
What Is a Seed Phrase and How Does It Relate to a Private Key?
You've probably heard the term seed phrase (also called a recovery phrase or mnemonic phrase). It's typically a set of 12 or 24 random words that looks something like this:
“witch collapse practice feed shame open despair creek road again ice least.”
A seed phrase is not the same as a private key, but it's closely related to one. It's essentially a human-readable backup that can regenerate your private key (and all associated keys in the wallet). Most software and hardware wallets use seed phrases as a recovery mechanism.
The tricky part: a seed phrase carries the same power as a private key. Anyone who gets hold of it has complete access to your funds. Writing it on a sticky note or saving it as a screenshot is just as risky as emailing your password to someone. And unlike a private key, a seed phrase is made up of common words, which makes it easier to write down, but also easier to steal if you're not careful. To learn more about how seed phrases and private keys relate at a technical level, read how to create a private key for a crypto wallet with and without a seed phrase.
Why You Should Never Share Your Private Key
This point deserves its own section because it's that important. No legitimate wallet, exchange, or support team will ever ask you for your private key. If someone does, whether via email, chat, a "support" call, or a website, it's a scam. Full stop.
Common tricks scammers use:
- Fake customer support asking you to "verify" your wallet
- Phishing websites that look like legitimate wallet apps
- Social media DMs offering to help with a "stuck" transaction
- Browser extensions or apps designed to steal key data
Sharing your private key even once means permanently losing control of your wallet. The blockchain is immutable, so if someone uses your key to make a transaction, it can't be reversed.
Where and How Should You Store a Private Key?
This is where most people make costly mistakes. Here's what to avoid and what actually works.
What NOT to Do
- Don't store it in cloud storage (Google Drive, iCloud, Dropbox). If your account gets compromised, so does your key.
- Don't take a screenshot and save it to your phone. Photo rolls sync to the cloud automatically.
- Don't email it to yourself. Email is not a secure storage medium.
- Don't save it in a notes app. Most are cloud-backed by default.
- Don't store it on a centralized exchange. When crypto lives on an exchange, you're trusting the exchange with custody. They hold the keys, not you.
- Don't type it into a form or website unless you are 100% certain of the source.
What Actually Works
Hardware wallets are the gold standard. A hardware wallet is a physical device that stores your private key offline, meaning it's never exposed to the internet or the malware-ridden world of connected devices. Your key lives inside the device's secure chip and signs transactions locally, without ever leaving the device.
Metal backup plates for seed phrases are worth considering if you use a seed phrase-based wallet. Paper can degrade, burn, or get wet. Etching your seed phrase into steel is significantly more durable, and storing it in multiple secure locations for backups. Keeping one copy at home and one in a safety deposit box is a reasonable approach for seed phrase storage.
Hot Wallets vs. Cold Wallets: A Quick Overview
You'll often hear these terms when talking about private key security.
Hot wallets are connected to the internet, browser extensions like MetaMask, mobile apps, or exchange accounts. They're convenient for frequent transactions but are more exposed to hacking, phishing, and malware.
Cold wallets (or cold storage) keep your private key completely offline. Hardware wallets fall into this category. The tradeoff is that they're slightly less convenient to use on the fly, but the security advantage is massive.
For anything beyond a small amount you're actively trading, cold storage is the smarter choice.
How Tangem Wallet Solves the Private Key Problem
Most of the complexity around private key security comes down to one fundamental issue: the key has to exist somewhere, and wherever it exists, it can potentially be exposed or lost. Traditional approaches either make you memorize a seed phrase (risky if written down carelessly), store a key in software (vulnerable to malware), or trust a third party like an exchange (you're not actually in control).
The Key Never Leaves the Card
Tangem is a hardware wallet that looks like a credit card. When you first set it up, the card's chip generates a private key using a certified hardware True Random Number Generator (TRNG) built into the chip itself. The key is stored exclusively within that secure element and never leaves the card under any circumstances. Not even Tangem can access it. Not if the card is stolen. Not if you contact their support. The architecture physically prevents extraction.
The chip is a Samsung Semiconductor secure element certified to EAL6+, the same security standard used in international passports and banking systems. Independent security firms Kudelski Security and Riscure both audited Tangem's firmware and confirmed that there are no backdoors, vulnerabilities, or ways to compromise the key.
No Seed Phrase Required (By Default)
Here, Tangem stands out from most alternatives. The default setup requires no seed phrase. Instead, you can back up your private key by cloning it across two or three Tangem cards using an encrypted, mutually authenticated process. No plain text. No words written on paper. No phishing risk. Each card in the set provides identical access to your funds, like having three identical keys to the same vault. Lose one card, and the others still work. You can store them in different locations for added protection.
If you prefer a traditional seed phrase, Tangem supports importing one. The phrase is converted to a private key and stored in the chip, but bear in mind that seed phrases are inherently a weaker link; they can be photographed, copied, or found. The seedless default is genuinely more secure.
You Sign Transactions by Tapping Your Phone
To send crypto, you open the Tangem app on your phone, set up the transaction, and tap the card to your phone via NFC. The card signs the transaction internally and returns only the digital signature to the app. The private key itself stays inside the chip throughout.
This design removes the most common attack vectors: there's no desktop software, no USB connection, no seed phrase entry on a potentially compromised computer, and no cloud sync. Because Tangem has no screen, you verify transaction details on your phone rather than on the card itself, which means you rely on your phone’s display to show accurate transaction data. It's a real tradeoff, though, for the vast majority of users who just want simple, secure storage; it's a reasonable one.
Built for Real People, Not Just Tech Experts
Most hardware wallets have a learning curve. Tangem is genuinely different. It fits in your pocket like a card, needs no charging, works with any NFC-compatible smartphone, and you can complete the setup in minutes with no technical experience.
It's not trying to be the most complex wallet on the market. It's trying to be the one most people will actually use correctly, which, in security, often matters more than theoretical maximum protection, and is very affordable for every common person. For a deeper look at how Tangem handles key backup, check out how Tangem Wallet backs up private keys.
Common Private Key Mistakes and How to Avoid Them
Mistake | Why It's Dangerous | Better Approach |
Storing the key digitally on the phone | Cloud sync exposes it | Hardware wallet or encrypted offline storage |
Using an exchange as a wallet | Exchange controls your key | Self-custody wallet |
Sharing the key with "support." | Classic scam tactic | Legitimate services never ask for it |
One backup location | Theft, fire, and flood can destroy it | Multiple geographically separated backups |
Typing the seed phrase into a website | It may be a phishing site | Never enter seed phrases online |
Using a weak random number generator | Attackers can crack predictable keys. | Use hardware wallets with certified TRNG |
Frequently Asked Questions
What happens if I lose my private key?
You permanently lose access to the funds in that wallet. There is no recovery option, no customer support that can help, and no way to reverse it, which makes secure backup non-negotiable.
Can someone guess my private key?
In theory, yes. In practice, it's functionally impossible. A Bitcoin private key has 2^256 possible combinations; a number that dwarfs the number of atoms in the observable universe. A supercomputer running forever couldn't brute force it.
Is my private key the same as my wallet password?
No. Your wallet password or PIN protects access to the wallet app or device. Your private key is the cryptographic key that actually controls your funds on the blockchain. These are different things.
Can I have multiple private keys?
Yes. Most modern wallets generate many key pairs from a single seed phrase using an HD (Hierarchical Deterministic) wallet structure. Each blockchain address you use has its own key pair, all derived from one master key.
What's the difference between a private key and a seed phrase?
A seed phrase is a human-readable backup that can regenerate your private key (and all derived keys). A private key is the actual cryptographic value used to sign transactions. The seed phrase produces the private key; the private key controls your funds. You must protect both with equal care.
Is it safe to store crypto on an exchange?
It's convenient, but the exchange holds your private key, not you. This means you're trusting them with your funds. Exchanges can be hacked, go bankrupt, or freeze withdrawals. For anything significant, self-custody with a hardware wallet is safer.
What does "not your keys, not your coins" mean?
It's a popular phrase in the crypto world that captures one simple truth: if you don't hold the private key, you don't truly own the crypto. You have a claim against whoever holds it, but you're not in direct control.
How does Tangem protect my private key without a seed phrase?
Tangem generates the private key inside the card's secure chip using a hardware random number generator. The key never leaves the chip. Backup is handled by cloning the key to additional Tangem cards over an encrypted connection; no seed phrase is involved, and no opportunity for interception in plain text.
Can Tangem access my private key?
No. The private key is stored inside the card's secure element and physically cannot be extracted; not by Tangem, not by a thief, not by anyone. Two independent security audits have verified this.
What if I lose my Tangem card?
If you have a backup card (Tangem sells 2- and 3-card sets), you still have full access to your funds. If you lose all cards without a backup, you lose access to that wallet, which is why we strongly recommend the multi-card backup setup.
Final Thoughts
A private key is the single most important piece of information in your crypto life. It's what proves you own your funds and allows you to move them. If you lose it, you lose the funds. If you share it, someone can steal it. If you store it carelessly, a single breach can wipe you out.
The good news is that protecting a private key doesn't have to be complicated. Tools like Tangem Wallet have genuinely simplified the problem by removing the seed phrase from the equation and keeping the key locked inside a certified hardware chip, all in something small enough to carry in your wallet alongside your ID. Understanding how private keys work is step one. Protecting yours properly is step two; both matter. For more on private key security best practices, read how to store and use a private key safely.