How Tangem Wallet backs up private keys
Core Insights
The article explains how Tangem Wallet provides a secure alternative to traditional seed phrase backups for cryptocurrency wallets, which are vulnerable if exposed. Instead, Tangem uses a hardware-based method that allows users to clone their private key onto backup cards through a secure, mutually authenticated, and encrypted process leveraging unique card keys and Diffie–Hellman key exchange. This approach ensures that private keys are never exposed during backup, greatly reducing the risk of theft or unauthorized access.To ensure you don’t forfeit access to your cryptocurrency if you lose your crypto wallet, you’ll need to back up your private key by creating copies. This is usually done with the help of a seed phrase. The issue, however, is that seed phrases are extremely unsafe because anybody who gets their hands on one can use them.
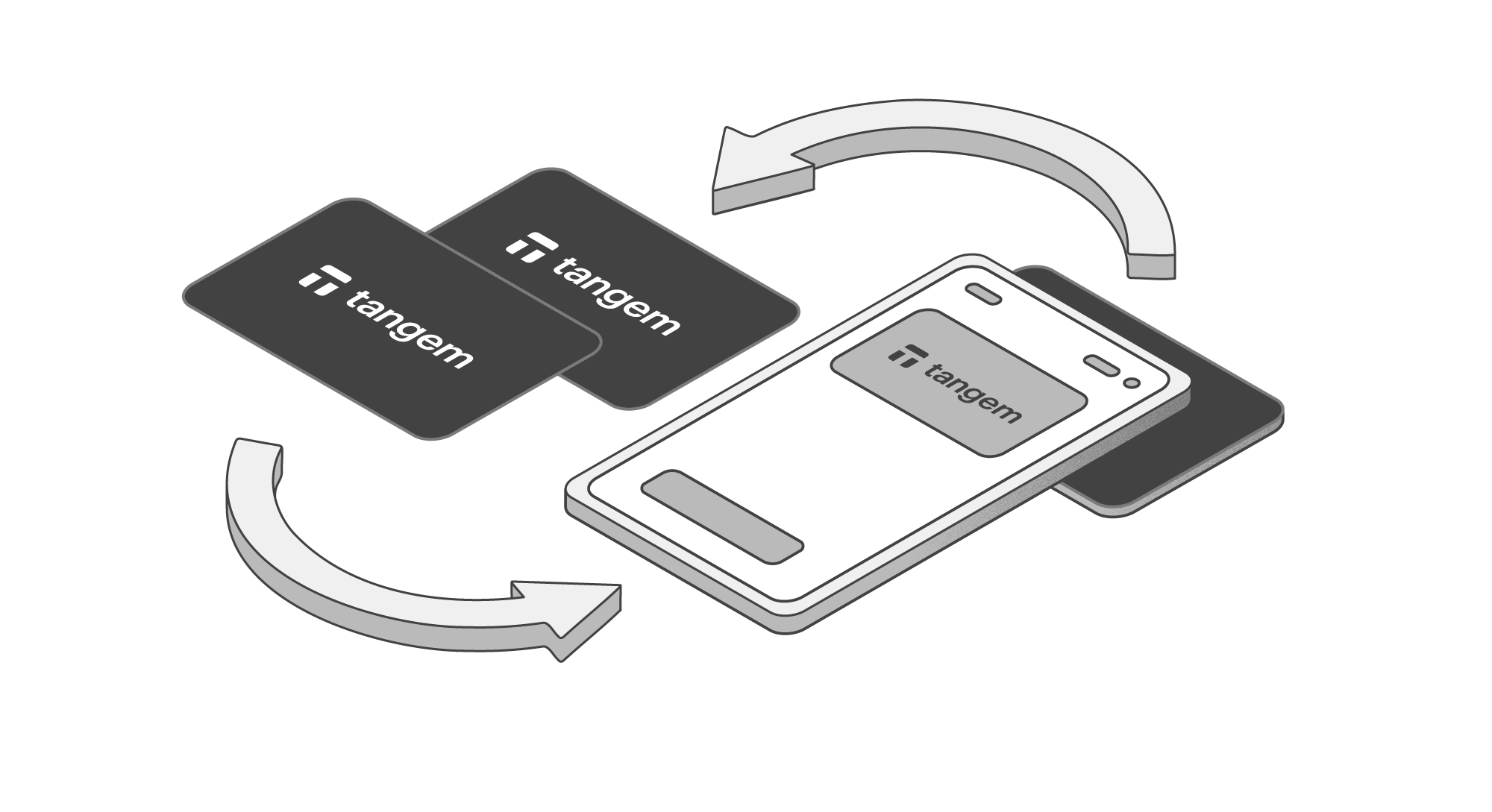
This is why Tangem Wallet offers a secure private key cloning solution. You can clone your private key to one or two backup Tangem cards without worrying that one of them will be lost or stolen.
But how safe is this backup method? Let's examine how Tangem Wallet accomplishes this.
Creating a private key
Initially, before the activation process, Tangem Wallet doesn’t have a private key (Kpriv, as shown in the diagram). When you purchase a Tangem Wallet, you’ll receive a package that hasn’t been activated yet and doesn’t have a private key, so you can be entirely sure that there aren’t any instances of the key unaccounted for anywhere in the world. After all, you can’t make a copy of something that doesn’t exist.
During the wallet activation process, the Tangem chip generates a new private key based on a numerical sequence received from a certified hardware random number generator (TRNG, as shown in the diagram). To learn how this process works, read our article How to create a private key for a crypto wallet with and without a seed phrase.
During this stage, there is only one instance of the private key. After that, you’ll need to create one or two copies as a backup, which must be done securely.
Preparing to create a backup
During the backup process, the private key must be transferred to the other cards in such a way that prevents it from being stolen, and the user must retain full control over the number of copies of the private key that exist.
For this reason, the private key backup process consists of two subtasks:
- First, you need to make absolutely sure that the key will be transferred to another Tangem card.
- The key must be protected from any interception while transmitting it to the other card(s), which means it must be encrypted so that only the receiving card can decrypt it.
When the card is produced at the factory, the chip generates its own key pair: the Kcardpriv private key and the Kcardpub public key. These keys are unique to each card and are in no way connected to the wallet of the future card user. They are only required so that the card can prove its authenticity and tell the app that Tangem produced it.
The public key from this pair is signed by Tangem using the manufacturer’s private key, KTangempriv. The resulting Cert_Card certificate is then used to validate the card.
The manufacturer’s public key, KTangempub, is also written onto the chip. This key is the same for all cards and forms the starting point of a “chain of trust” between the source and destination card.

The first challenge: Mutual authentication
For each card to be “sure” that the card on the other end is a genuine Tangem Wallet card during the backup process, a cryptographic “chain of trust” must be built out of the cards’ keys and signatures.
During activation, each card creates a single-use key pair to communicate with the other cards – Klinkpub and Klinkpriv – and signs the public key from this pair with its Kcardpriv private key, creating the Sign_Attest signature.

The card then sends the Sign_Attest, Klinkpub, and Kcardpub information to the other card.
This process creates the following chain of trust: KTangempub — Kcardpub — Klinkpub. The manufacturer’s public key, KTangempub, is known to every card, and each of them uses it to verify the Cert_Card certificate. If it matches the other card’s Kcardpub, then this key is used to verify the Sign_Attest signature of that card.
If Sign_Attest matches the other card’s Klinkpub, it means the card on the other side of the communication channel was genuinely produced by Tangem, and that nobody has modified its Klinkpub key. It can be used to calculate the shared Ktrans backup key.

The second challenge: obtaining a shared encryption key
At this stage, both cards need to generate a shared symmetric key, Ktrans, which the source card will use to encrypt the user's private key, while the destination card will decrypt it. Since the communication channel between them is provided by an untrusted device, it’s impossible to simply generate a key in one card and transfer it to another. This issue is solved by using the Diffie–Hellman key protocol.
The cards have just exchanged the verified and trusted Klinkpub keys, with each card using its own Klinkpriv and the other card’s Klinkpub to generate the symmetric Ktrans encryption key, which ends up being identical for both cards. This is the magic of Diffie–Hellman in action.
Additionally, if an attacker takes control of the user’s phone and can “eavesdrop” on the card exchange, they will only find out the Klinkpub and Kcardpub public keys because these are the only things transmitted by the cards. The Klinkpriv keys will remain inaccessible, meaning that the attacker won’t be able to generate the same Ktrans.

Encrypted key exchange
Using the Ktrans symmetric key it has obtained, the first card encrypts a data set containing the user’s private key and access code, as well as the number of private key backups (set of 2 or 3 cards).
The card sends the resulting encrypted ENC message to the second card, which decrypts it using the same Ktrans. If anybody managed to intercept the ENC at this moment, they wouldn’t be able to find out anything because, without the Ktrans key, they cannot decrypt the package.

The procedure for completing the backup for the third card is precisely the same; however, the cards generate new Klink pairs, meaning that the Ktrans key differs from the one used when backing up onto the second card.
The Tangem chip firmware allows for one backup to be completed. After giving or receiving a private key, the card will cease to initiate the backup procedure, and the private key will be unrecoverable.
If you perform a factory reset on your Tangem wallet, the chip will forget the Kpriv key. You can then reactivate the wallet, generate a new key, and complete a new backup. Be aware, however, that the old key will be destroyed after the reset.