
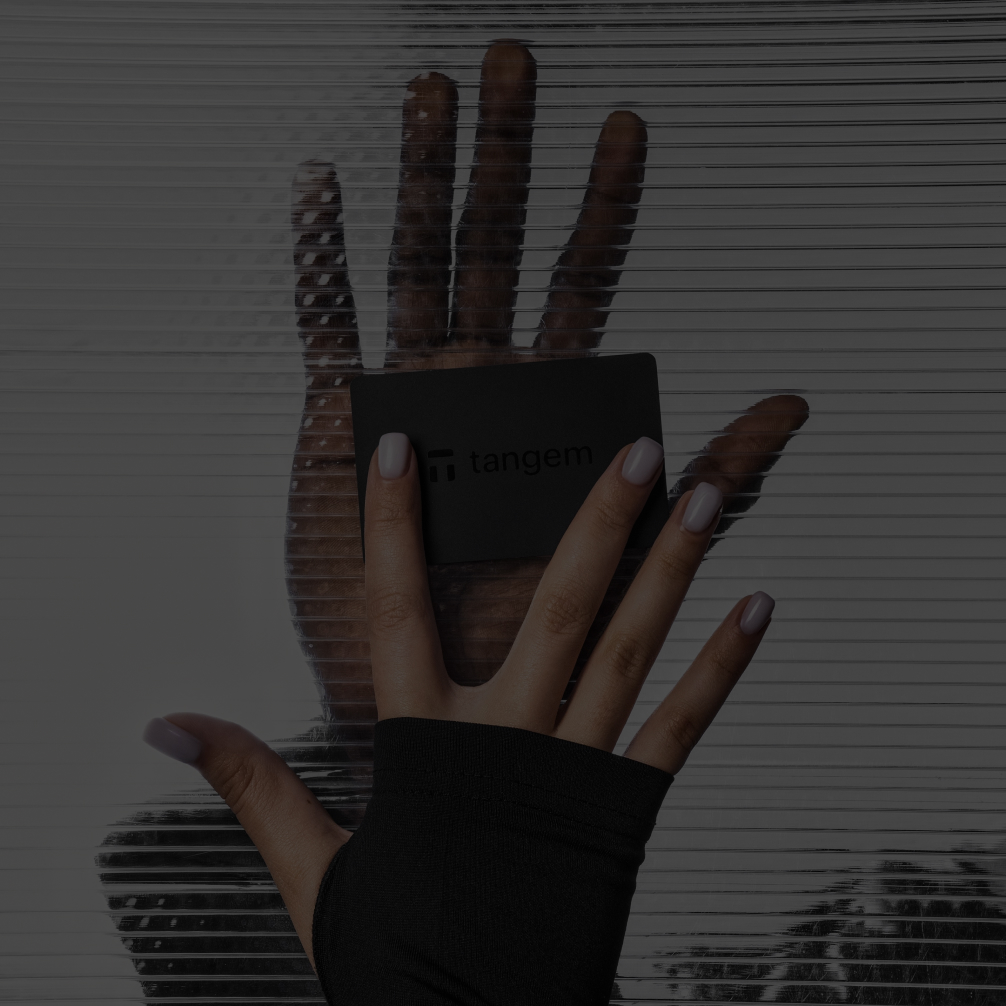
Tangem。あなたのウォレット。
銀行カードのようにスリムで、銀行の金庫のように安全です。何千種類もの暗号資産を保存、購入、獲得、転送、交換できます。
- スイス拠点
- 25年保証
- EAL6+セキュリティ規格
- Kudelski Security社により監査済み
Tangemは、世界最高水準のセキュリティ、シンプルさ、アクセシビリティを提供することで、暗号資産ウォレットの利用体験を再定義します。 ワンタップで暗号資産を管理しながら、完全な自律性と独立性をお楽しみいただけます。 Tangemウォレットは、暗号資産初心者への壁を取り除き、上級ユーザーの体験を向上させます。
Tangemは、世界最高水準のセキュリティ、シンプルさ、アクセシビリティを提供することで、暗号資産ウォレットの利用体験を再定義します。 ワンタップで暗号資産を管理しながら、完全な自律性と独立性をお楽しみいただけます。 Tangemウォレットは、暗号資産初心者への壁を取り除き、上級ユーザーの体験を向上させます。
Tangemカードをスマートフォンにタッチするだけで、Tangemウォレットを利用できます。



スマートなバックアップ
- カードに内蔵されたチップにより、ランダムな秘密鍵が生成されます。その秘密鍵が公開されることはありません。
- カードは互いに安全な接続を確立し、暗号化された秘密鍵を転送します。
- 秘密鍵は3枚のカードに保存され、コピーは不可能です。
Tangemアプリなら暗号資産を最大限に活用できます。
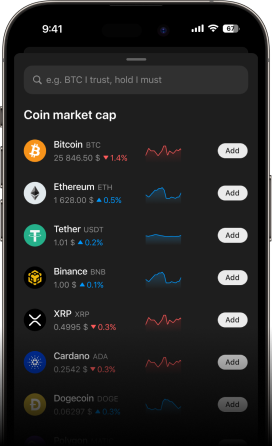
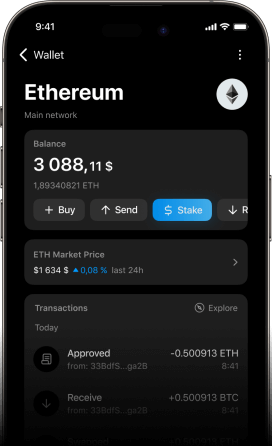
何千もの暗号資産のデータにアクセス可能。価格を比較し、より多くの情報に基づいた投資の意思決定を行えます。
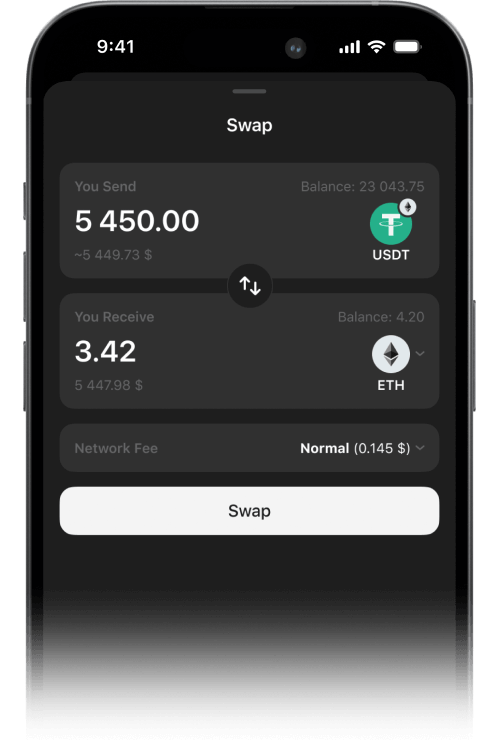
当社のプロバイダーで、暗号資産を素早く安全にスワップ(交換)することができます。ポートフォリオを分散し、資産を保護することができます。
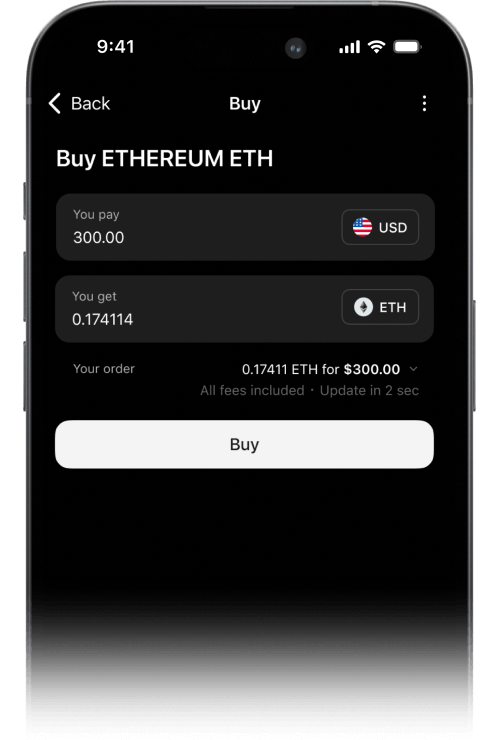
クレジット カード、銀行振込、Apple Pay、Google Payで、ビットコインやその他の暗号資産を簡単に購入できます。
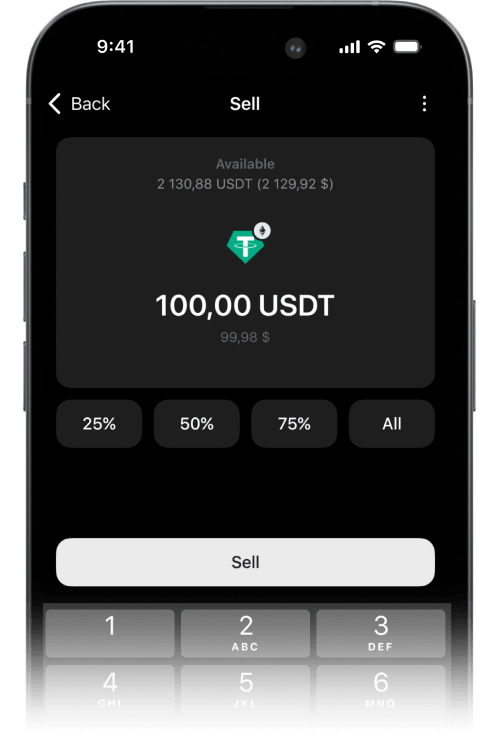
複数のオプションを使用して、ビットコイン、イーサリアム、その他の暗号資産を安全に売却できます。
イーサリアム(ETH)、ソラナ(SOL)、コスモス(ATOM)などをステーキングして、資産を受動的に増やせます。
数千種類の暗号資産にアクセスできます
Tangemチップについて
Tangemウォレットは、サムスン電子と共同開発した強力な認証チップを搭載。すべてのカードは、1x1mmのマイクロコンピュータの形をしたチップを内蔵しています。
- 最高水準のチップセキュリティ。あらゆる攻撃から暗号資産を保護します。
- 頑丈。水や極端な温度(-25度〜50度)への耐性があります。
- 環境耐性。X線、電磁パルス、静電気放電の影響を受けません。
- アンテナ付きのチップ。脆弱性や障害の発生を抑えることが可能です。
- 偽造防止。Tangemアプリにより、チップとファームウェアの両方の信頼性が認証されます。
- すぐ利用可能。充電は必要ありません。

つながりを保ちましょう。
私たちの進歩や最新の更新を見逃さないでください。影響を与える — 今日私たちのコミュニティに参加しましょう!
信頼に基づく選択。




Ivan On Tech
50万人の登録者







質問にお答えします。
- ハードウェア暗号通貨ウォレットを所有する主なメリットは、セキュリティが強化されることです。秘密鍵はオフラインでデバイスに保存されるため、ハッキング攻撃やコンピュータに感染するマルウェアの影響を受けにくくなります。そのため、盗難や詐欺によって暗号資産を失うリスクが軽減されます。 もうひとつの大きなメリットは、自分自身で完全にコントロールできることです。自分の鍵は自分で所有し、第三者の許可なくいつでも暗号資産を使用することが可能です。
- シンプルさと安全性です。 Tangemウォレットはいつでも持ち歩くことができ、充電や有線接続は必要ありません。Tangemカードは他のクレジットカードと一緒に持ち運べ、どこでも取引に署名できます。Tangemウォレットは使い方も非常に簡単です。お使いのスマートフォンでカードをタップするだけで、暗号資産にアクセスできます。 利便性だけでなく、TangemカードのEAL6+認証チップは生体認証パスポートと同じくらい安全です。他のハードウェアウォレットは専門家によってつくられた専門家向けのウォレットだとすると、Tangemウォレットはシンプルさと高度なセキュリティを組み合わせて、すべての人のために作られたものです。
- カード3枚セットなら、2枚セットよりもウォレットへのアクセスを回復できる可能性が高くなります。例えば、1枚のカードを紛失したり盗まれたりしても、もう1枚のカードでウォレットにアクセスできます。ただし、1枚のカードを紛失してアクセスコードも忘れてしまった場合、アクセスコードをリセットするために3枚目のカードが必要になります。そのため、3枚セットを取得することをお勧めします。
- 世界最高水準の技術を駆使し、当社は完全自律型の暗号資産ウォレットを設計しました。Tangemサーバーはいかなる場合においても、お客様の暗号資産の管理に関与したり、アクセスすることはありません。そこにあるのは、お客様のカード・スマートフォン・ブロックチェーンだけです。TangemアプリのコードはGitHubで入手できるため、たとえAppleやGoogleによってアプリストアから削除されても再構築することができます。
- いいえ。Tangemウォレットは、アクセスコードによって第三者からの不正アクセスや総当たり攻撃から保護されています。
- シードフレーズの使用は任意です。Tangemウォレット2.0で秘密鍵を生成するには3つの方法があります: 1. 認証済みTRNG(True Random Number Generator)を使い、秘密鍵を生成してカードチップに保存します(推奨)。Tangemを含め他の誰もこの情報にはアクセスできません。また、Tangemのカード以外からコピーが作られる心配もありません。 2. Tangemアプリでシードフレーズを生成し、カードにインポートします。 3. 他のウォレットからシードフレーズをインポートします。Tagemカードが生成する秘密鍵とは異なり、シードフレーズはコピーされたり盗まれたりする可能性があります。 シードフレーズ技術の詳細とTangemの意見についてはこちら
- いいえ、お客様の資金にアクセスできなくなることはありません。Tangemカードを使用して、別のスマートフォンからウォレットにアクセスできます。別のスマートフォンでTangemアプリをダウンロードし、カードをスキャンするだけです。 お客様のスマートフォンには機密情報は保存されません。スマートフォンは、簡単にアクセスするためのウォレットのUIにすぎません。Tangemウォレットは2台以上のスマートフォンで使用できます。ウォレットの秘密鍵はスマートフォンに保存されているため、携帯番号は関係ありません。
