How a blockchain transaction is validated
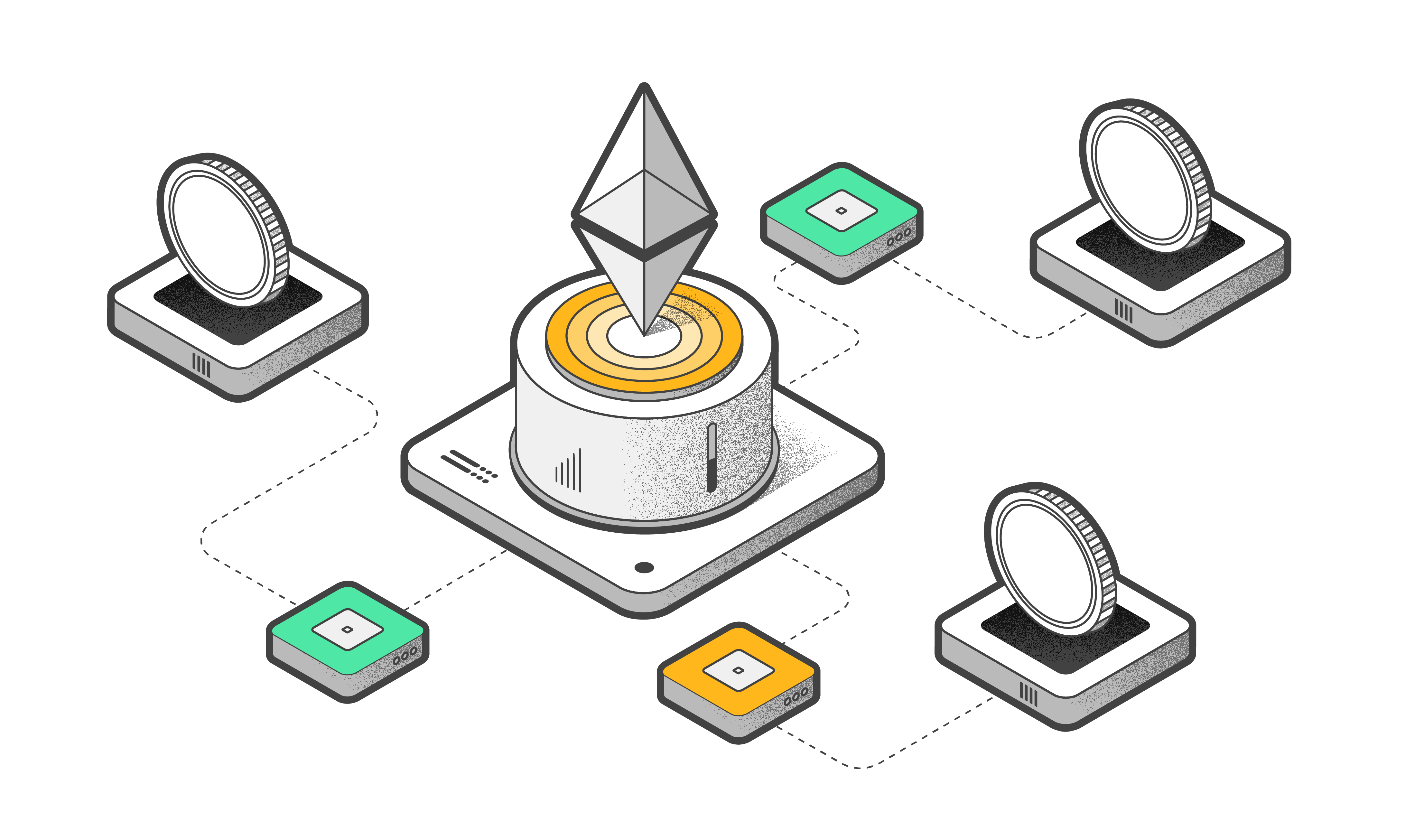
Several consensus mechanisms exist for validating blockchain transactions. The most popular one is Proof of Work (PoW), used for Bitcoin, Litecoin and most other blockchains. The consensus mechanism confirms that all nodes in the network have the same version of the blockchain.
A hash function is the key element of a blockchain. It is a mathematical function converting any data into a number (hash). A hash cannot be reversed back to the original data. But If you change one bit anywhere in the original data, the entire hash value changes.
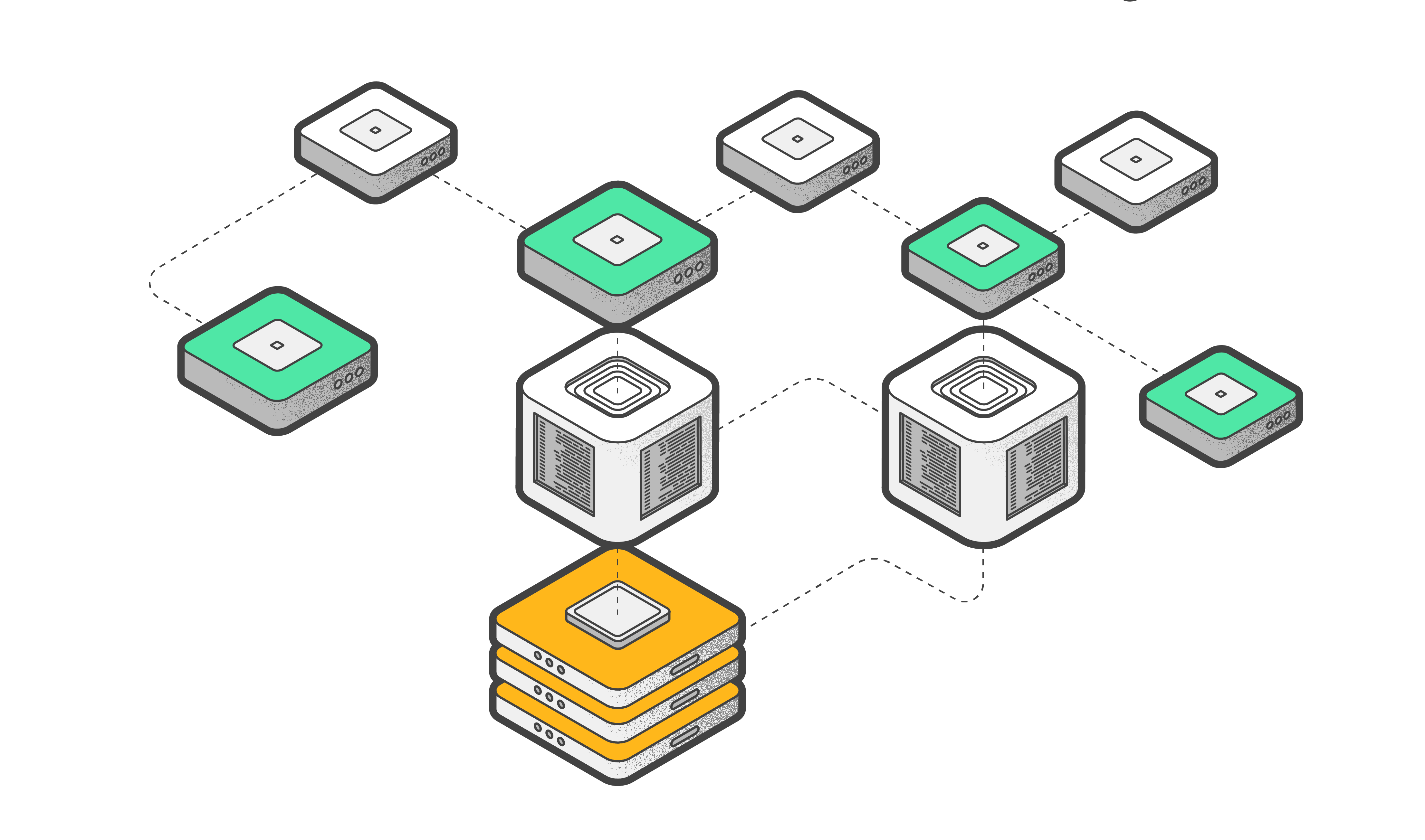
To put it simply: new transactions are added to a blockchain through a process of consensus. It means that the majority of nodes must agree that the transaction is valid.
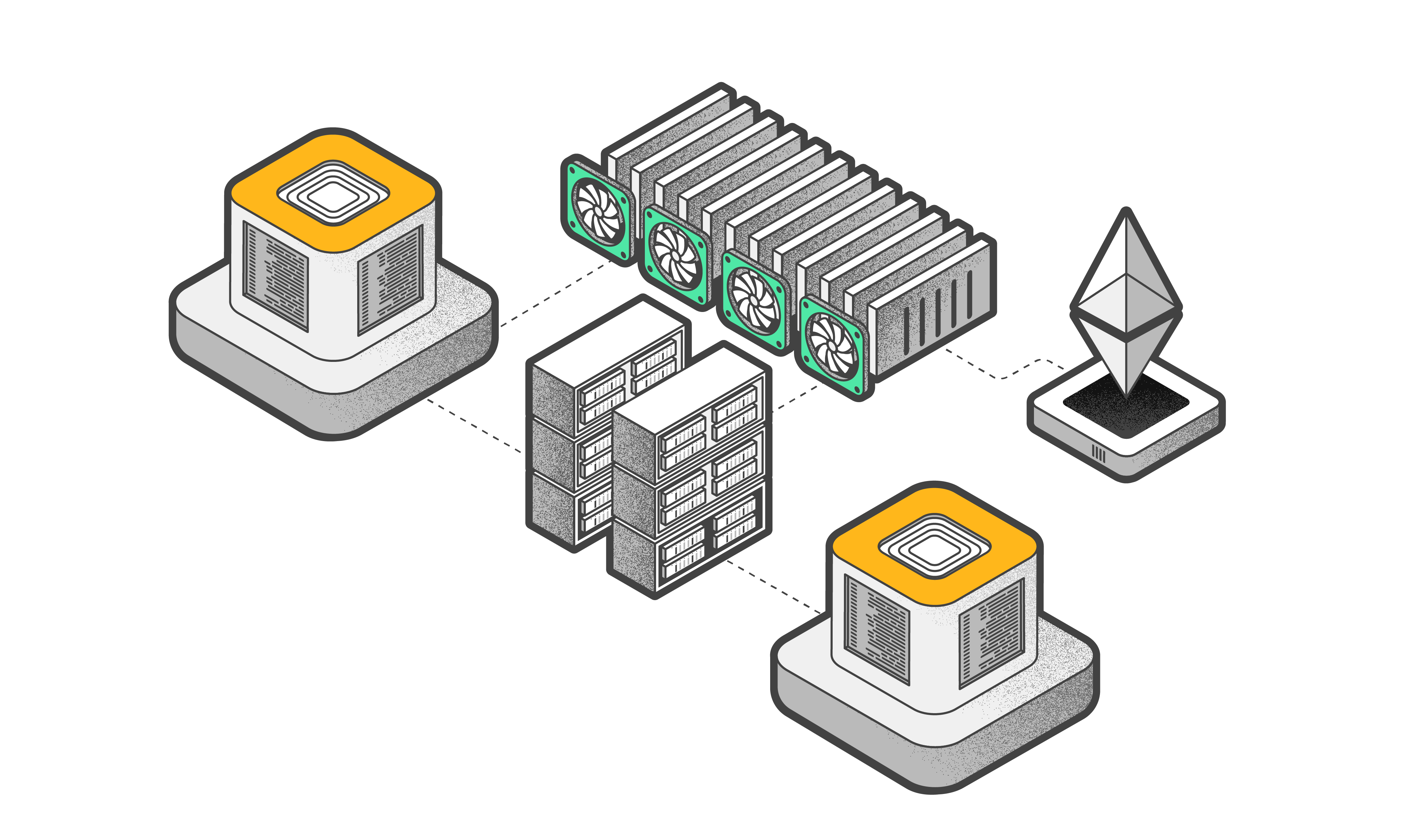
When you send a transaction to a blockchain, it is transmitted to all the mining nodes (or validators), and it goes to their mempools (waiting area). Each node aggregates a batch of transactions into a draft block for the blockchain and tries to mine it:
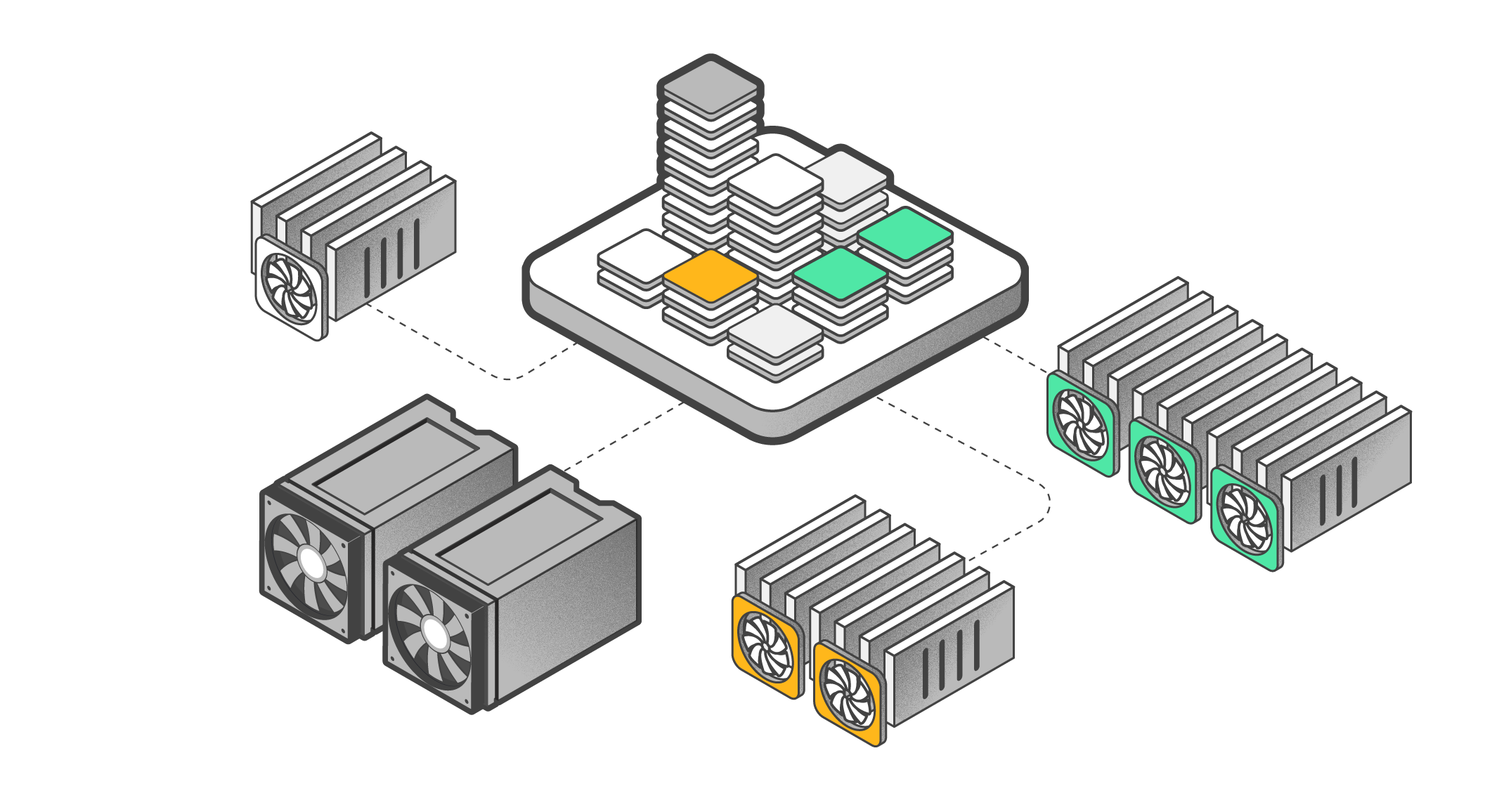
1. All the transactions in the block are summed up. This number is added to the hashed contents of the previous (final) block, which is then hashed.
2. The node compares the resulting hash to the current difficulty. Difficulty is a measure, a number to which each computed hash is compared. If the hash below a given target, the miner is lucky enough to have mined a block. If the hash exceeds the number, the miner increments the block by 1 and calculates the hash again. And so on millions of times per second.
3. As soon as a node has mined a new block, it transmits it to all other nodes. All other miners immediately stop trying to mine their blocks, include the new block into their version of the blockchain and begin forming the next draft block. Once the new block appears in the blockchains of several nodes, all transactions will be considered validated.
To put it simply: for creating a list of new transactions, a validating node solves a complex mathematical problem by brute force. Once the brute-force is successful, the transactions are included into a blockchain, while the other nodes interrupt their brute-force pocess, include the new transactions in their copy of the blockchain, and start a new brute-force process.

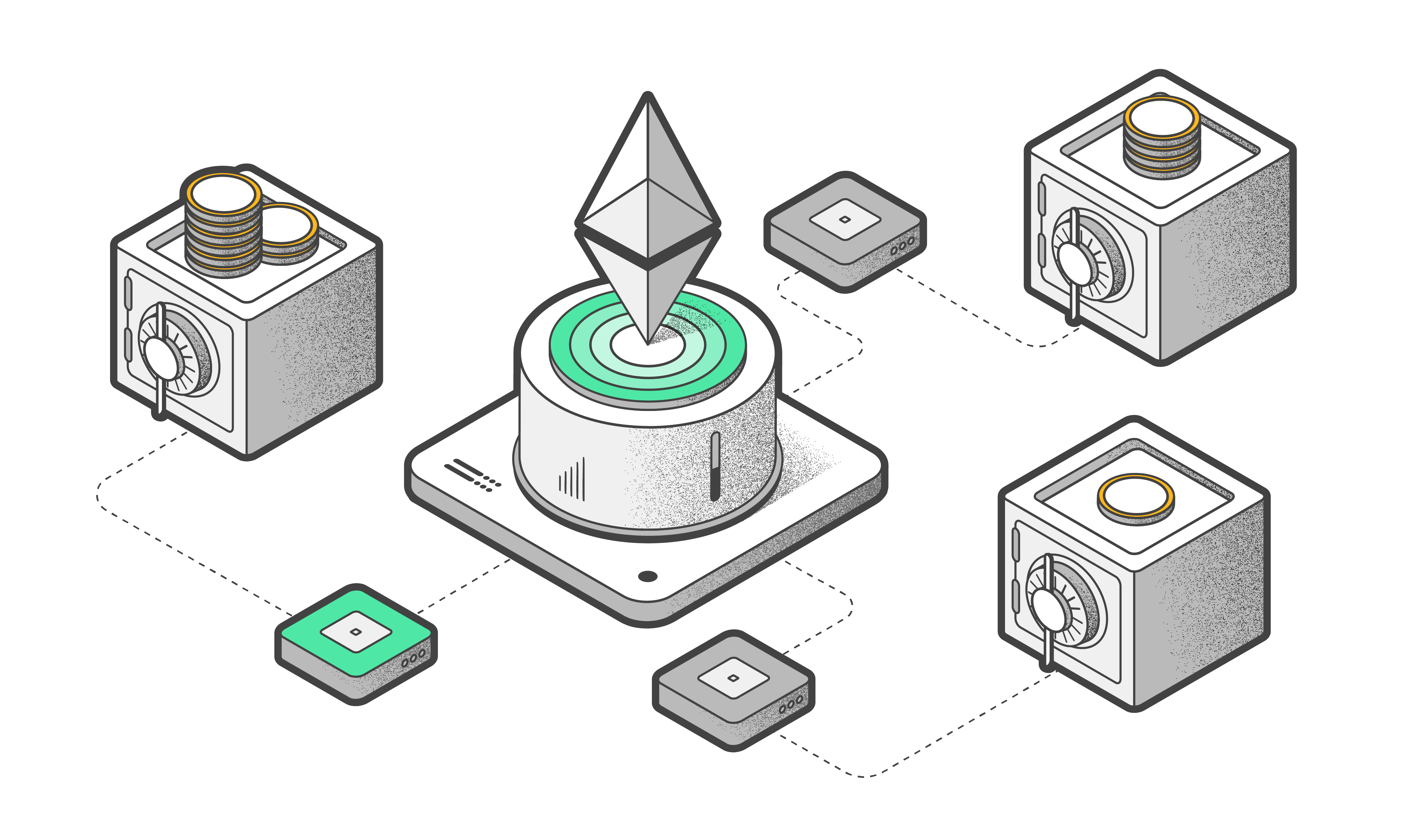
All of these sophisticated steps prevent an attack on the blockchain. For example, attackers could spend their cryptocurrencies and send the transactions to the network and then create new versions of a blockchain to spend the same cryptocurrency again. The attackers will then send their versions of the block to all the other nodes. It is like two versions of the blockchain emerge: in the first version the cryptocurrency is sent to one address, and another version has the same cryptocurrency sent to a different address.
Consensus mechanisms are developed to resolve this conflict. The process is simple: a node detecting a blockchain branch discards the shorter branch, the one with less blocks. An attacker is supposed to mine his blocks faster than the rest of the network for a tampered branch to become legitimate. The mining mechanism makes this extremely expensive in terms of processing power.
But if an attacker lacking processing powers fails, there are still chances some nodes could have managed to get the tampered block but not the real one. Therefore each service sets a certain number of confirmations required to consider a transaction completed. For small amounts, 1 to 3 confirmations are usually sufficient, while for transactions for millions of dollars worth of cryptocurrency, an exchange service would prefer to wait for several dozen confirmations before allowing the transaction.
To put it simply: new transactions shall be first verified by other servers. The difficulty of the mathematical problem prevents from making falsified transactions quickly.